A single jog recorded on a fitness app inadvertently revealed the precise location of France’s flagship aircraft carrier, highlighting the unforeseen security risks posed by popular digital tools in military operations.
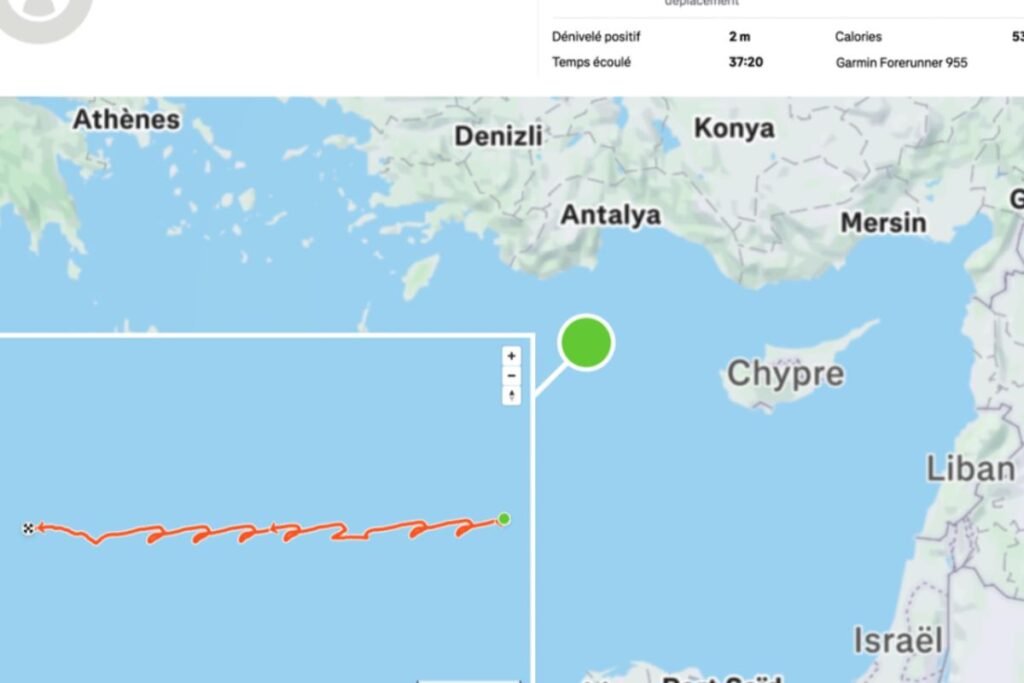
On March 13, 2026, an officer aboard the French nuclear-powered aircraft carrier Charles de Gaulle used the Strava app to track a run around the ship’s deck. Because his profile was public, this well-intentioned fitness activity became a beacon that pinpointed the vessel’s position northwest of Cyprus in the eastern Mediterranean, a region marked by high geopolitical tension. This event underscores how everyday technology can unintentionally compromise sensitive military assets during critical missions.
How a routine workout exposed a strategic military asset
The simplicity of the act—logging a 7-kilometer run in 35 minutes—belies the gravity of the outcome. While habits like sharing fitness data are common, doing so from a mobile navy vessel was a major security lapse. Investigators were able to cross-reference the jog’s GPS data with satellite imagery taken just over an hour later, confirming the ship’s unique 262-meter profile within a 6-kilometer radius of the recorded track.
Decoding the vulnerability in everyday apps
Strava, a popular sports tracking app, is designed to provide users with insights on their physical activity. However, it also broadcasts location data to anyone able to access a public profile. For the Charles de Gaulle, this translated into a real-time digital breadcrumb trail, compromising operational secrecy. This case is a pivotal example of how seemingly innocuous consumer technology may pose complex security challenges when used in military environments.
The wider implications for military cybersecurity discipline
This incident is far from isolated. Earlier reports revealed similar leaks from the protective details of national leaders and nuclear submarine patrols, all using the same fitness platform. The recurring pattern points to a broader issue concerning the enforcement of digital operational security, particularly regarding the use of civilian apps among military personnel.
Risks beyond the digital perimeter
Maintaining secure communications and classified protocols has long been a cornerstone of military discipline. Yet, the pervasive use of smartphones and connected devices blurs traditional lines. An app shared among millions worldwide becomes a weak link once used in active military zones. Public profiles and default sharing settings amplify the risk, allowing adversaries to gather intelligence piecemeal but precisely through open-source information.
Charles de Gaulle’s mission profile in a volatile region
The deployment of France’s only nuclear-powered aircraft carrier in the eastern Mediterranean was a deliberate response to intensifying regional conflicts and aimed at protecting French nationals and maritime security. Despite its defensive posture, the vessel’s location is of high strategic interest to international observers. Any leak, intentional or accidental, could provide rivals with sensitive data on France’s military readiness and deployment patterns.
Strategic sensitivity of naval asset positioning
The vessel’s movement through the Strait of Gibraltar into a hotspot near Cyprus underscores the delicate balance of naval power in the region. A carrier’s presence can signal political resolve or deter adversaries, so the exposure of its position through an app’s GPS data represents more than a simple privacy slip — it is a breach with potential tactical repercussions.
Examining the multifaceted risks of location exposure
The consequences of such digital leakage are varied but serious:
- Tactical risk: Real-time geolocation enables enemies to identify where a crucial military asset is deployed.
- Operational risk: Tracking patterns across multiple reported activities can reveal mission tempos and operational routines.
- Strategic risk: Gradual accumulation of such data can create a broader map of a nation’s military footprint and intentions.
From casual fitness tracking to a security breach: why the risk persists
Normalizing the use of civilian fitness apps among active military personnel creates a perception gap about privacy. Users often underestimate the potential visibility and aggregative power of location data, which can be easily combined with other open-source intelligence. The Charles de Gaulle incident highlights how unchecked digital habits may contradict military directives aimed at maintaining “combatant digital hygiene.”
Command responses and ongoing challenges
The French armed forces acknowledged the breach and reiterated ongoing education about secure app use among sailors. Statements confirmed that while such lapses violate existing guidelines, they revealed gaps in enforcement and individual awareness, emphasizing the need for enhanced digital discipline training. Nevertheless, monitoring and regulation of personal device usage in sensitive environments remain complex to implement fully.
Framework of dates and events related to Strava leaks involving military personnel
| Date | Event | Details |
|---|---|---|
| 2024 | StravaLeaks investigation | Revealed location data leaks from presidential security details via Strava. |
| January 2025 | Nuclear submarine crew leaks | Personnel inadvertently revealed patrol schedules through fitness tracking. |
| March 13, 2026 | Charles de Gaulle incident | Sailor’s public Strava run located the aircraft carrier in the eastern Mediterranean. |
Why does a fitness app pose a security risk for the military?
Fitness apps like Strava collect and share detailed location data, which can reveal the position and movements of military personnel and vessels if profiles are set to public.
What are the consequences of revealing an aircraft carrier’s location?
Exposing the location risks tactical disadvantages, allows adversaries to monitor mission patterns, and can compromise broader strategic military operations.
Has this type of security leak happened before?
Yes, similar incidents have occurred in 2024 with presidential security details and in 2025 involving nuclear submarine crews.
What measures are in place to prevent fitness app leaks?
Armed forces conduct regular training about digital security and combatant digital hygiene, but enforcing strict controls on personal device use remains challenging.
Could such leaks affect international relations?
Yes, unintentional disclosures of military positions can increase regional tensions and undermine diplomatic efforts by revealing sensitive strategic movements.
Source: https://www.lemonde.fr/international/article/2026/03/19/stravaleaks-le-porte-avions-charles-de-gaulle-localise-en-temps-reel-par-le-monde-grace-a-l-application-de-sport_6672445_3210.html

